Understanding CVSS Severity Levels and Ratings | Comple...
Learn what CVSS is, how it scores vulnerabilities, and what severity ratings like Low, Medium, High, and Critical mean. Stay infor...
What Is Power/Clock/Reset Glitching? Fault Injection Ex...
Learn what Power, Clock, and Reset glitching are in cybersecurity. Explore how these fault injection techniques help bypass embedd...
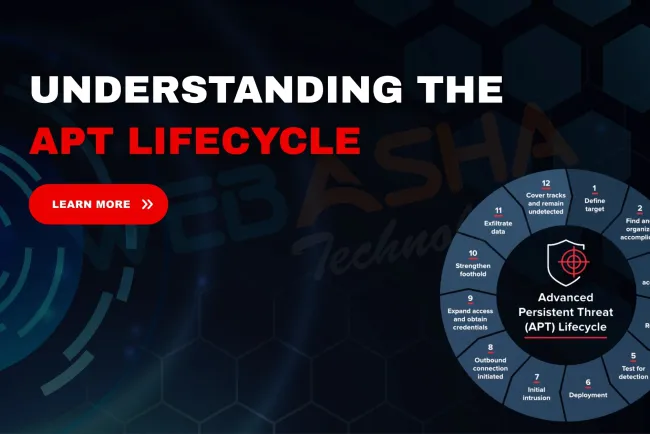
What Are the Steps of the APT Lifecycle? Full Guide to ...
Learn the 7 critical steps of the Advanced Persistent Threat (APT) lifecycle, including reconnaissance, privilege escalation, late...
What Is a Spear Phishing Attack? Examples, Prevention &...
Learn what a spear phishing attack is, how it differs from phishing, real-world examples, and expert strategies to detect and prev...
India’s First AI-Powered Blood Test Launched | Non-Inva...
Discover how India’s first AI-powered blood test is transforming healthcare with contactless, non-invasive diagnostics. Learn abou...
What is IDOR Vulnerability? Insecure Direct Object Refe...
Learn what an IDOR vulnerability is (Insecure Direct Object Reference), how attackers exploit it, real-world examples, and how to ...
Which of the Following Best Describes Code Injection? E...
Discover the correct definition of code injection, how it works, examples like SQL injection and XSS, real-world risks, and how to...
What is DNS and DNSSEC? Full Guide to How DNS Works and...
Discover what DNS (Domain Name System) is, how it powers internet browsing, and why DNSSEC (DNS Security Extensions) is critical f...
How Encryption Helps Attackers Evade NIDS Detection on ...
Learn how attackers use encryption to bypass NIDS on compromised Linux servers. Understand real-world tactics, NIDS limitations, a...
What is the Boot Sector Virus | How It Works, Real Exa...
Learn what a boot sector virus is, how it infects systems, real-world examples like Michelangelo, how to detect, prevent, and remo...
Kismet | The Best Wireless Packet Sniffer & IDS for 802...
Discover why Kismet is the top wireless LAN sniffer, network detector, and IDS for 802.11(a/b/g/n) networks. Learn how it works, w...
How Blind SQL Injection Works | Scenario with Time-Base...
Discover how blind SQL injection works using a real-world CEH training example. Learn how time-based SQLi can help you detect vuln...
How to Create Strong Passwords Without Losing Your Mind...
Learn how to create strong, secure, and memorable passwords with ease. This guide covers password best practices, examples, tips, ...
How I Failed My First Red Team Engagement and What I Le...
Discover the real story of a red teamer’s first failed engagement. Learn key lessons on stealth, reporting, coordination, and tool...
Why Every Hacker Must Learn the MITRE ATT&CK Framework ...
Discover why the MITRE ATT&CK Framework is essential for ethical hackers and Red Teamers. Learn its benefits, tactics, real-world ...


















![Top 10 Ethical Hackers in the World [2025]](https://www.webasha.com/blog/uploads/images/202408/image_100x75_66c2f983c207b.webp)



![[2025] Top 100+ VAPT Interview Questions and Answers](https://www.webasha.com/blog/uploads/images/image_100x75_6512b1e4b64f7.jpg)






