Tag: cybersecurity
The Top Eight Kali Linux Tools For 2025
Discover the essential Kali Linux tools for cybersecurity professionals and ethical hackers in 2023. Explore the features and modu...
Learn Ethical Hacking from Scratch | A Comprehensive Gu...
Discover how to become an ethical hacker with our comprehensive guide. Learn the skills, knowledge, and certifications needed to p...
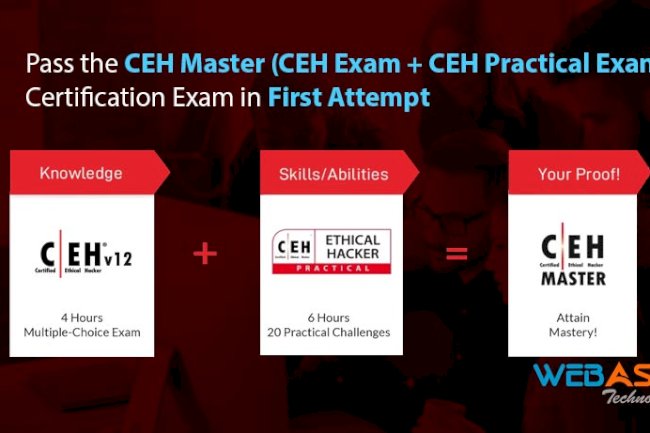
How To Pass the CEH Master (CEH Exam + CEH Practical Ex...
Looking to become a Certified Ethical Hacker Master? This guide will provide you with tips and strategies to help you pass both th...
How To Pass the Certified Ethical Hacking CEH v12 Certi...
Learn important study tips and take advantage of resources from WebAsha Technologies to pass the Certified Ethical Hacking (CEH) v...
10 Important Tips to Clear CEH Exam in First Attempt - ...
Clearing the CEH exam in the first attempt can be challenging. This expert guide provides 10 important tips for effective preparat...
Ethical Hacker Resume Samples for Working Professional ...
Craft a winning resume as an ethical hacker with 3-5 years of experience using our sample templates. Showcase your skills and achi...
What is Cybersecurity and Why is Cybersecurity Importan...
Cybersecurity is a combination of computer network defense and information assurance. Computer networks consist of various types o...









![Top 10 Ethical Hackers in the World [2025]](https://www.webasha.com/blog/uploads/images/202408/image_100x75_66c2f983c207b.webp)


![[2025] Top 100+ VAPT Interview Questions and Answers](https://www.webasha.com/blog/uploads/images/image_100x75_6512b1e4b64f7.jpg)







